## Modern microservice implementation
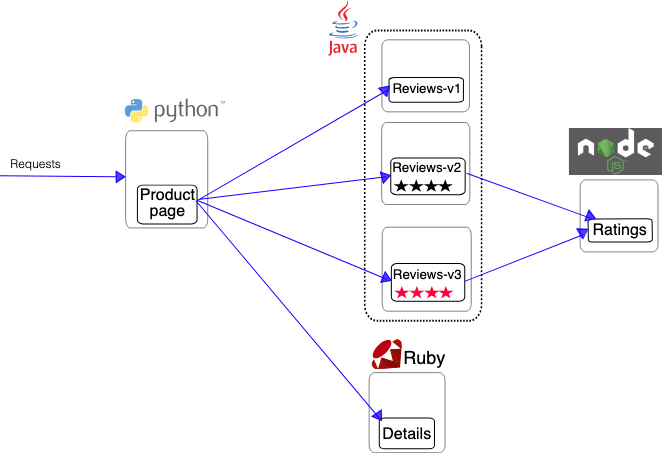
Typically, as the microservice project progresses, naturally we have to manage three types of connections:
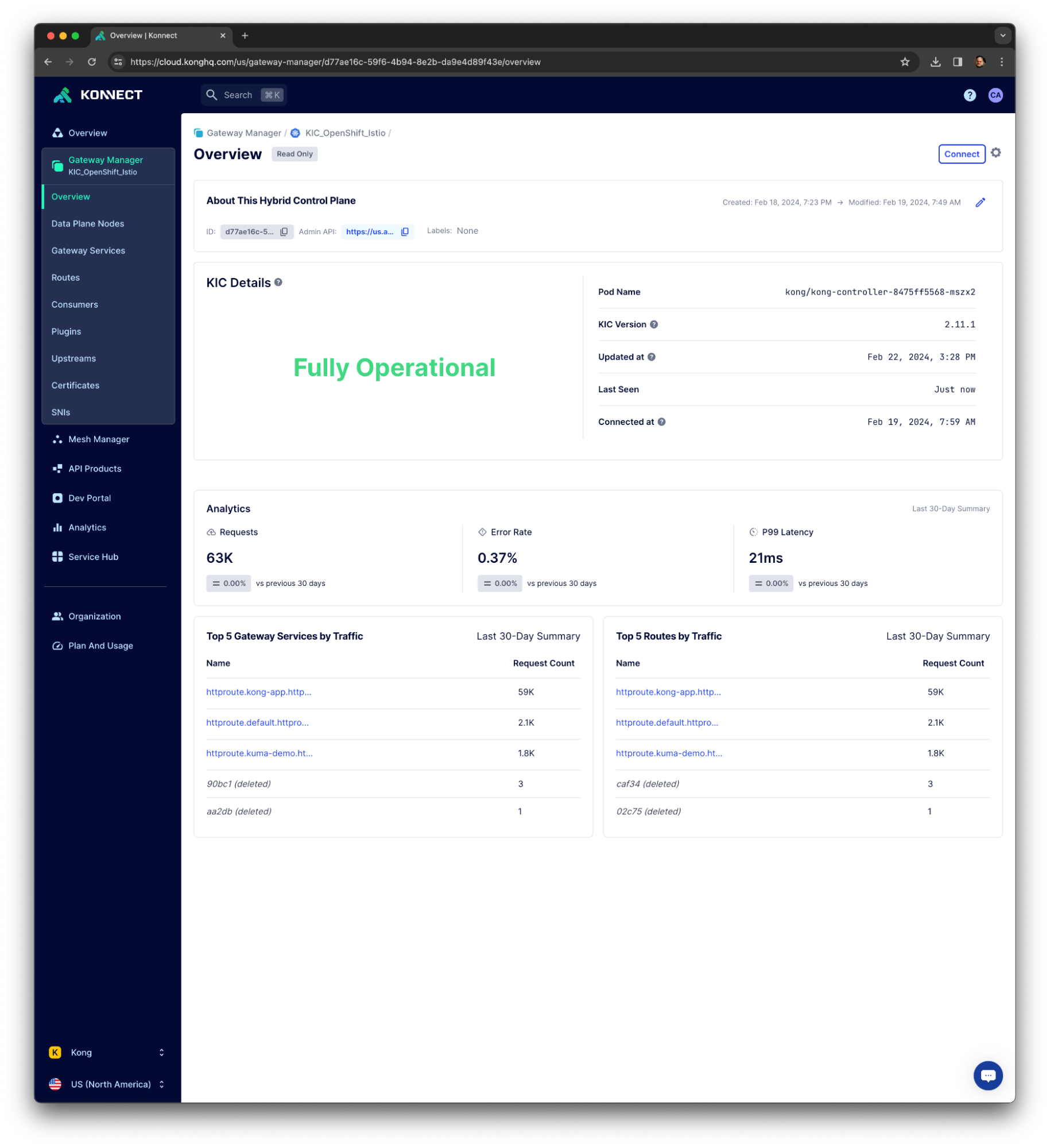
- - **Edge connectivity**: This is the traffic we receive from external consumers. This connectivity is implemented and controlled by Kong Ingress Controller (KIC).
- - **Cross-app connectivity**: Applications will talk to each other, so it’s important to control this communication as well. Another instance of KIC is deployed to control it with specific and application-oriented policies. Note: This isn’t depicted in the diagram.
- - **In-app connectivity**: This is where the service-to-service connectivity is implemented by the service mesh.
## Service mesh and ingress controller policies
In an enterprise-class application environment, typically, we have policies defined in both layers. Generally speaking, the ingress controller should be responsible for coarse-grained policies controlling the application consumption as the service mesh controls the fine-grained policies related to the microservices.
A good example could be the authentication and authorization processes. While the authentication processes tend to be implemented in a centralized environment, typically by the ingress controller, microservices authorization processes are inherently distributed. Typically, there are two levels of abstraction for access control policies:
- - **Low granularity**: This is focused on generic security policies. For example, access time, service required, IP address of the request, etc. The ingress controller layer also handles this authorization level.
- - **High granularity**: This is access control performed by microservices in relation to their specific resources. For example: operation within a service (read or write). The service mesh typically implements this authorization level.
In summary, we, as business and technical architects, should be able to define multiple policies in both layers.
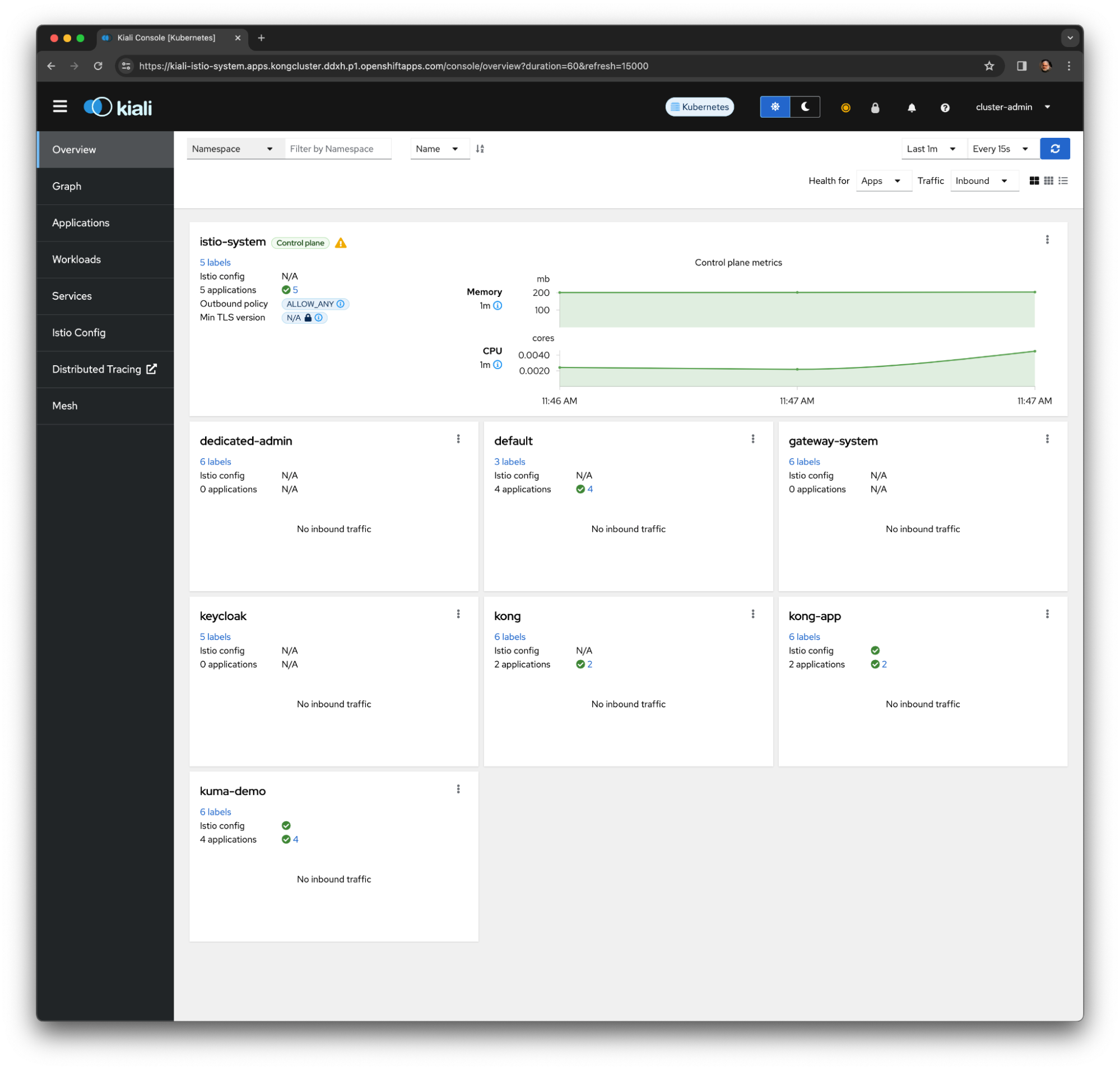
Red Hat OCP is available on-prem bare metal or virtualized, Amazon Web Services (AWS), Google Cloud Platform (GCP), IBM Cloud, Microsoft Azure, Nutanix, Red Hat OpenStack Platform, VMware Cloud (VMC) on AWS. It’s also available as a managed service on major public cloud providers.
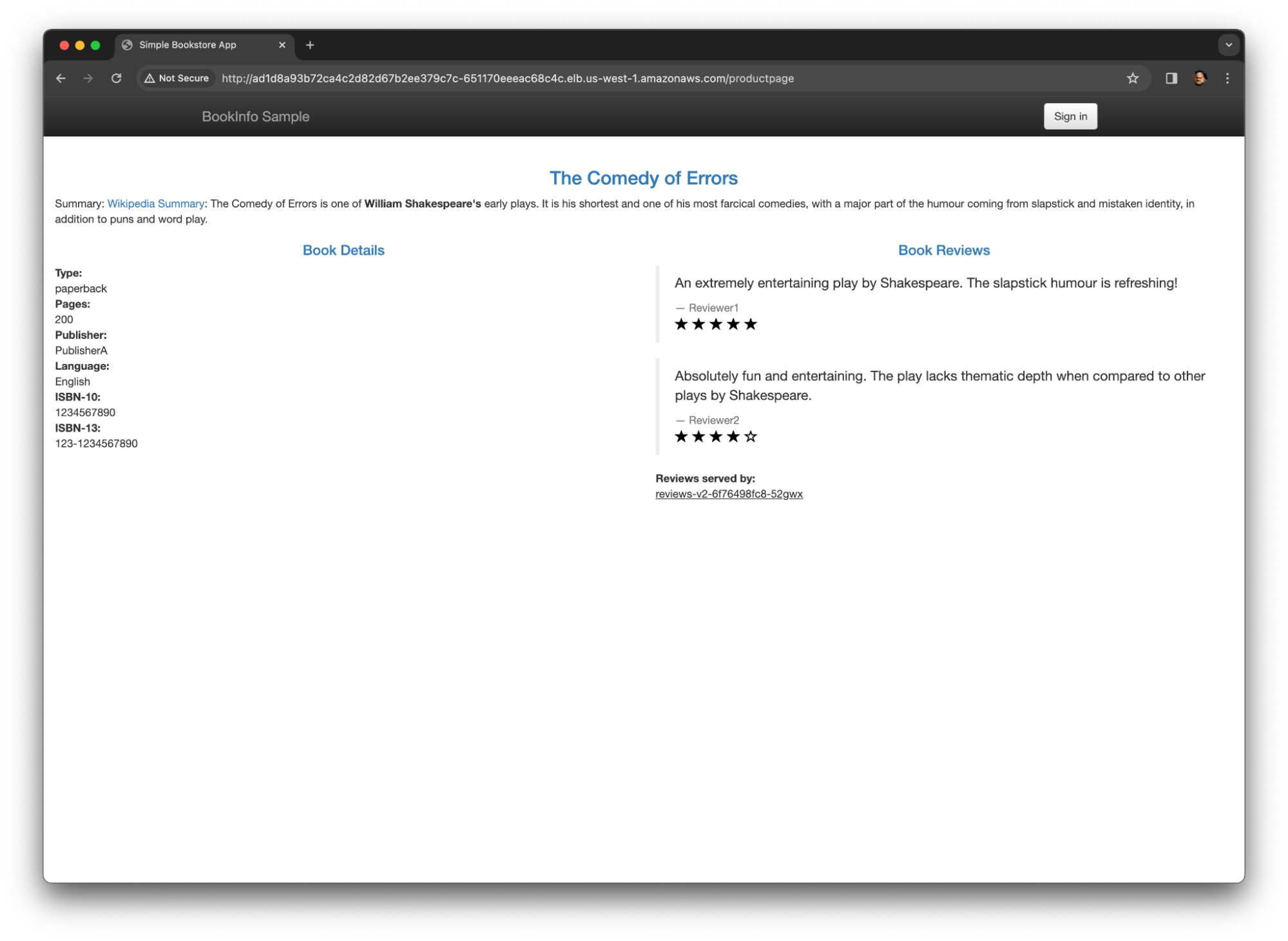
As an example, here's the OCP console after installing Red Hat OpenShift Service on AWS ([ROSA](https://www.redhat.com/en/technologies/cloud-computing/openshift/aws)ROSA):