In the digital age, a top-notch API gateway must not only be reliable and secure but also bring robust governance and security features designed for enterprise needs. The new [Kong Gateway 3.3 for Open Source](https://konghq.com/blog/product-releases/kong-gateway-3-3-open-source)Kong Gateway 3.3 for Open Source comes with robust enhancements such as configurable queuing behavior, high-scale reliability with readiness probes, and notable improvements to the OpenTelemetry plugin. These capabilities, which are central to our offerings, set the foundation and are included in our enterprise versions.
In this post, we'll further explore the Kong Gateway 3.3 advanced and exclusive features introduced in Kong Enterprise and Kong Konnect.
## **OpenAPI Spec for Kong Enterprise**
Kong is thrilled to announce an OpenAPI Spec (OAS) for the Kong Enterprise admin API. OAS specs are critical for organizations as they navigate and consume APIs. They provide a single source of truth as to the shape of a given API that is referenceable by all who consume the API.
By providing a machine-readable, easily shareable specification, we encourage third-party developers and partners to leverage our APIs creatively. Moreover, embracing an OpenAPI spec reinforces our commitment to transparency and open standards.
View all of Kong's published specs at [developer.konghq.com.](https://developer.konghq.com/)developer.konghq.com.
## Software Bill of Materials (SBOM) Kong KonnectEnterprise
In a move to further bolster software security and enhance transparency, every new release of Kong Enterprise now includes a Software Bill of Materials (SBOM). An SBOM is essentially a comprehensive record of the various components that make up a software product. These components can be anything from open-source libraries, third-party software, or proprietary code.
By incorporating SBOMs, Kong Enterprise provides in-depth insights into the third-party components used in our software. This increased transparency allows users to not only understand the building blocks of our software but also facilitates effective management and compliance with licensing requirements.
Moreover, SBOMs can be crucial in ensuring adherence to specific industry standards or regulations that might apply to the software. For instance, security-focused regulations may necessitate a comprehensive understanding of all software components, a need that SBOMs directly address.
To offer flexibility and ease of use, we'll provide SBOMs in two widely adopted and industry-recognized formats:[ cycloneDX](https://cyclonedx.org/) cycloneDX and[ SPDX](https://spdx.dev/) SPDX. Both of these formats are designed to accurately document and communicate the components used in a software product, thus aiding in software transparency, license compliance, and security analysis.
Starting in Kong Enterprise 3.3 and for all following Kong Enterprises releases you can find the associated SBOM in our documentation under ‘Software Bill of Materials.'
Click[ here](https://docs.konghq.com/gateway/latest/support/sbom/) here to get the SBOM for the 3.3 release. SBOMs are more than equipped to provide you with the necessary resources and support to ensure your organization benefits from this added layer of transparency and security.
### AWS/Aurora Authentication with DB IAM Auth Enterprise
One of the standout enhancements of Kong Enterprise 3.3 is the inclusion of support for [AWS Identity and Access Management (IAM) database](https://docs.aws.amazon.com/AmazonRDS/latest/AuroraUserGuide/UsingWithRDS.IAMDBAuth.html)AWS Identity and Access Management (IAM) database authentication. This feature specifically caters to users of DB-backed instances of Kong who seek to establish connections to Amazon Aurora or Amazon Relational Database Service (RDS) as their database for Kong Enterprise configuration.
This integration significantly expands the potential of Kong Enterprise, allowing organizations to leverage the powerful capabilities of AWS’s IAM service. Not only does this feature enhance the overall security architecture of the applications running on AWS, but it also presents a centralized platform for access management, thereby streamlining operations and reducing the complexities traditionally associated with multiple access management systems.
Furthermore, the use of IAM database authentication for connections with AWS Aurora or RDS bolsters the security of network traffic via encryption. This function serves to protect sensitive data and communication, thereby ensuring that information remains confidential and protected during transmission.
By enabling AWS IAM authentication, Kong Enterprise 3.3 offers organizations a more robust, secure, and streamlined system for managing their API gateways. This integration signifies our commitment to not only respond to the evolving needs of our users but also stay ahead of the curve in the increasingly complex digital landscape. It's part of our constant push to deliver more innovative, efficient, and secure solutions for our user base, and a reflection of our dedication to driving the future of the API gateway space.
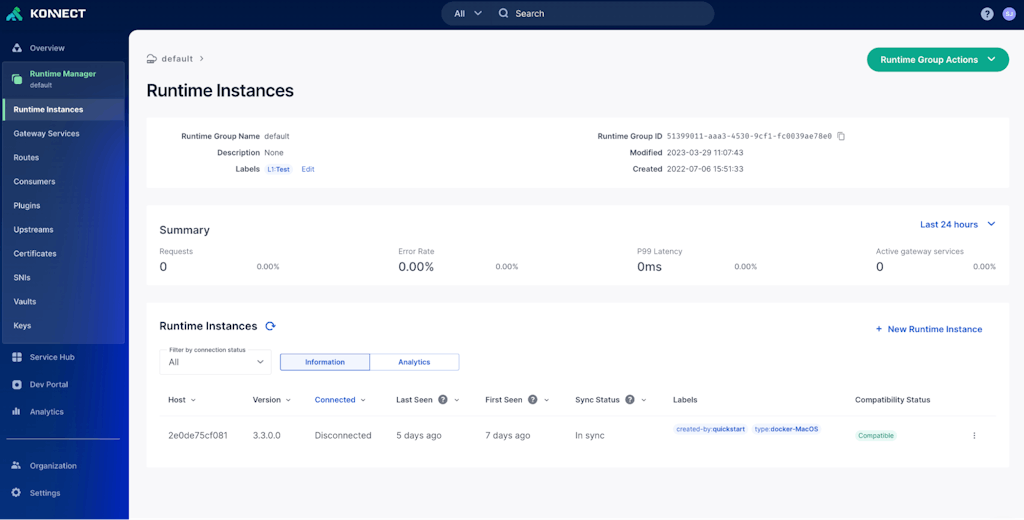
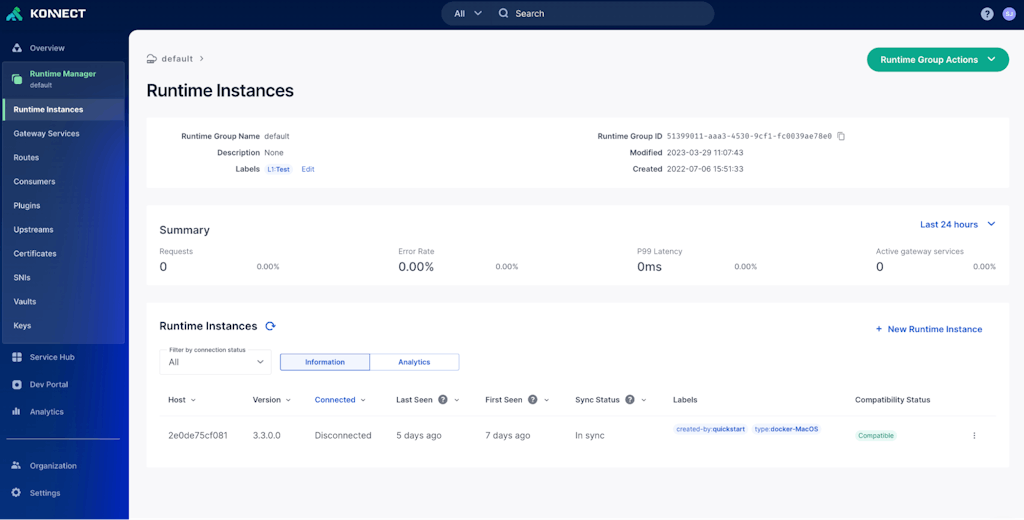
### Association of data plane metadata Kong Konnect
The Kong Konnect platform now allows users to associate metadata with their Kong Gateway data planes within a runtime group.
Users can define key-value pairs within the Konnect interface. These key-value pairs are set on the data planes and propagated up to Konnect, providing a powerful tool for categorizing and managing clusters of data planes across an organization. Examples of data plane labels that can be used are as follows:
- - Cloud provider or cloud provider region in which a single DP runs
- - Business line owner/contact for a particular DP
- - DP image version for customers who create their own images
This feature enriches the governance you get in Kong Konnect by adding useful details about individual DPs within a runtime group. Additional details can be found[ here](https://docs.konghq.com/konnect/runtime-manager/runtime-instances/custom-dp-labels/) here.
In the image below you'll see the Konnect UI, which we call Runtime Manager. It lists all of your ‘Runtime Instances', which in this case are connected Kong Enterprise gateways. This feature powers the brand new ‘labels' column in this view below.
### Get started today
[Sign up for Kong Konnect](https://konghq.com/products/kong-konnect/register)Sign up for Kong Konnect for free and get started today with Kong Gateway 3.3!
If you're interested in Kong Enterprise 3.3 you can download it for free [here](https://konghq.com/install)here. If you have Kong Gateway installed already, upgrading to 3.3 is easy. Check out our [upgrade guide](https://docs.konghq.com/gateway/latest/upgrade/#main)upgrade guide.
For a full list of features, fixes, and updates, please see the available CHANGELOG for Kong Enterprise [here](https://docs.konghq.com/gateway/changelog/)here and Kong Gateway OSS [here](https://github.com/Kong/kong/blob/master/CHANGELOG.md#330)here.