# 3 Solutions for Avoiding Plain-Text Passwords in Insomnia
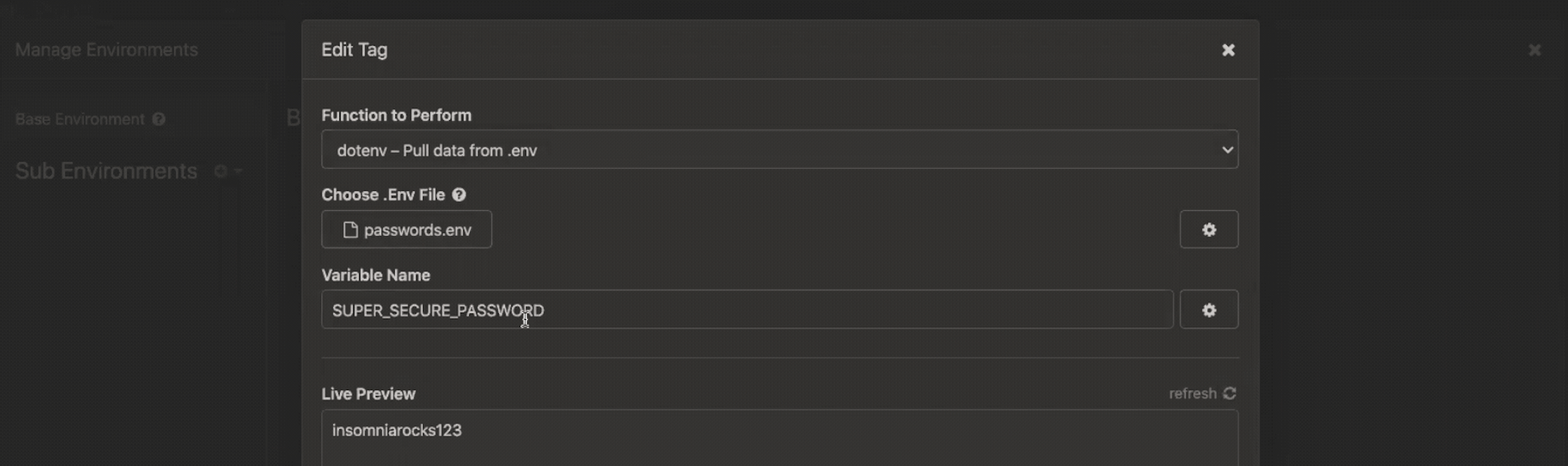
When testing APIs, software engineers often repeat identical values across multiple requests, but who wants to waste time typing the same values every time? Insomnia 's environment variables solve this problem by allowing you to define a value once as an environment variable and reference that…
[](/blog/engineering/avoiding-plain-text-passwords-insomnia)